Prerequisites
ATS Bus depends on the following services to be installed and available:
ATS Security, ATS Licensing, ATS Bus and other ATS services require a valid certificate to encrypt the connections.
For further details, visit Certificates for TLS/SSL Connections and consult the IT team to obtain and install a valid certificate on the computer systems that will host the ATS applications and services.
SQL Server 2019 or newer is required by ATS Bus, ATS Security and ATS Licensing to persist configuration, security, and license information.
ATS Bus requires the SQL server instance to support SQL authentication.
ATS Bus, ATS Security and ATS Licensing connection strings can be enriched with the Encrypt and TrustServerCertificate properties to connect successfully to SQL Server. Use these properties in the event of an SQL connection related error message.
Microsoft has changed the default value for the ‘Encrypt’ property from ‘False’ to ‘True’ and therefore existing connection strings must be updated and include ‘Encrypt=False’ when the previous connection string did not include the ‘Encrypt’ property to compensate for the change and maintain the same behaviour prior to the update. Also note that ATS Bus configuration data like NServiceBus transport and persistence and IT and OT database channels must be updated when connecting to an SQL server database. Updating the connection strings is a manual step, there is no automated database migration that adds ‘Encrypt=False’ to the connection string.
RabbitMQ and Erlang are required when the ATS Bus transport is set to RabbitMQ. It is recommended to install RabbitMQ version 4.1.4 or newer and Erlang 26.2 or 27.
The user configured by the RabbitMQ transport requires the Policymaker permission to be set which allows users to create unlimited delivery limit policies through the RabbitMQ management API. Configuring the Policymaker permission is done in the RabbitMQ managment interface:
Login to the RabbitMQ Management interface
Click on the Admin menu and click on Users.
Click on the atsbus user and scroll to the bottom of the newly opened window.
Select the Policymaker tag, provide the password twice and press Update user. This sets the Policymaker permission for the atsbus user.
For more information on permissions in RabbitMQ, please click here.
Please visit the RabbitMQ transport documentation for more background information here.
For further information on the supported versions of Erlang, please click here.
Download RabbitMQ
Download Erlang
RabbitMQ management API access is required for the latest version of ATS Bus. This API is provided by the Rabbit MQ management plugin which can be installed using the rabbitmq-plugins tool. It can be found in the sbin subdirectory of the RabbitMQ installation directory. Run the command: rabbitmq-plugins enable rabbitmq_management to install the RabbitMQ management API and management web console. The web console is accessible via http://localhost:15672 (user guest, password: guest)
The RabbitMQ connection string must include a virtual host to separate ATS Bus from other applications or other ATS Bus installations.
Previous versions of ATS Bus used RabbitMQ without configuring a virtual host like:
host=rabbithost.domain.local;usetls=false;username=atsbus;password=atsbus;
Newer versions should use:
host=rabbithost.domain.local;usetls=false;username=atsbus;password=atsbus;virtualhost=/vhost1;
ServiceControl, ServiceInsight and ServicePulse are required to monitor ATS Bus services (bus stops).
Download Particular
ATS Bus 3.4 requires the following versions:
• ServiceControl 6.7.2 or higher.
• ServiceInsight 2.13.1 or higher.
• ServicePulse 2.1.1 or higher.
Install and configure ServiceControl, ServicePulse and ServiceInsight
ATS Security and Configuration version 2.0 or higher.
Install ATS Security and Configuration
ATS Licensing version 4.1 or higher.
Anti-virus software will affect the performance of ATS Bus, SQL Server or Particular ServiceControl by locking and scanning files used by these services. Also, applications like Dynatrace and Carbon Black may affect the performance of ATS Bus or its accompanying services. Consult with the IT and security department to exclude the following directories from on-access scanning:
ATS Bus installation directory
ATS Bus program data directory
ServiceControl program data directory that contains the RavenDB audit and error databases.
SQL Server data directory.
Any directory used by the ATS Bus configuration
All ATS products can be downloaded from the link below:
Certificates for TLS/SSL Connections
ATS Security, ATS Licensing, ATS Bus services configure certificates to encrypt the connection. A valid certificate should meet the following requirements:
It should be signed by a trusted authority.
It should not be expired.
It should have a valid trust chain.
The SAN extension should contain the name of the host that is hosting the service.
The enhanced key usage should be set to Client Authentication (1.3.6.1.5.5.7.3.2) and Server Authentication (1.3.6.1.5.5.7.3.1).
The certificate should be stored in the Personal folder of the Local Computer certificate store otherwise the installers and services are unable to find the certificate.
Certificates are used by the following ATS Bus features:
ATS Bus data service. The data service uses the certificate configured in the Kestrel section of the appsettings.json file. The installer selects it from the Personal folder of the local computer certificate store.
The OT, IT and ADOS bus stops configure a default certificate in the Kestrel section of the appsettings.json file. This certificate is configured by the installer and comes from the Personal folder of the local computer certificate store. This certificate is used for the IT and OT web service server channels, the ADOS Inspect Event channel and the ADOS Inspect web API channel.
Current versions of ATS Bus configure the certificate in the Kestrel section of the appsettings.json file. Older versions of ATS Bus (3.2 and older) bound the certificate to a port using netsh. ATS Bus does not need these bindings anymore and should be removed. Use ‘netsh http show sslcert ipport=0.0.0.0:9704’ to verify if a certificate is bound to a port (e.g. 9704) and use ‘netsh http remove sslcert ipport=0.0.0.0:9704’ to remove the binding (in this case from port 9704). Maintaining the binding might lead to unexpected results.
Always restart the ATS Bus services when certificates are renewed.
Install and configure ServiceControl, ServicePulse and ServiceInsight
ATS Bus uses ServiceControl, ServiceInsight and ServicePulse provided by Particular Software to monitor the bus stops and the messaging framework. ServiceInsight shows the messages being handled and failed and it also shows the message details. ServicePulse is used to monitor the message throughput and other performance related items.
ServiceInsight: Diagnostics tool showing messages and conversations. Uses ServiceControl to view all handled messages.
ServicePulse: A health monitor for the bus stops (production monitoring). It processes heartbeat messages from the bus stops and it allows the user to resend failed messages.
ServiceControl: Backend/service that provides information for ServiceInsight and ServicePulse. It's the central service that handles and processes the audit and error messages. The bus stops have a module/library that connects to the ServiceControl service.
ServiceControl, ServiceInsight and ServicePulse are tools and services that provide insights in the ATS Bus message handling:
ServiceControl is the backend for ServicePulse and ServiceInsight and collects audit, error, and monitoring data. It also retains the information for a preconfigured amount of time.
ServiceInsight, a diagnostics tool, shows the content of the messages being handled and failed.
ServicePulse: A health monitor for the bus stops (production monitoring). It processes heartbeat messages from the bus stops, and it allows the user to resend failed messages.
For further information on ServiceControl, please click here.
ServiceControl is provided as a portable application named ServiceControl Management Utility (a.k.a. SCMU) which installs and configures the ServiceControl instances. Please backup the portable application to a directory on the server that will host the ServiceControl instances.
ServiceInsight and ServicePulse are installed using classic installers. The installation and configuration steps are described in the following links:
• ServiceInsight
• ServicePulse
ServiceControl instances must configure the same transport as ATS Bus meaning that ServiceControl should configure RabbitMQ transport if ATS Bus configures RabbitMQ transport too. The NServiceBus configuration items, including the transport configuration is explained in ‘Configure NServiceBus‘. Read this paragraph and follow the links for more detailed information about the supported NServiceBus transport options.
Configuring and installing SQL Server, RabbitMQ, Azure Storage queues and Azure Service Bus is beyond the scope of this installation manual.
Follow the steps provided in the next paragraphs Setup a Monitoring Instance and Setup an Error and Audit Instance to quickly deploy the required ServiceControl instances once ServiceControl, ServiceInsight and ServicePulse are installed. Alternatively, visit the following pages for detailed information about installing and upgrading the ServiceControl instances:
Pay attention to the retention times when configuring the error and audit services as it affects the amount of disk space used to store audit and error messages.
Add or Update NServiceBus license to ServiceControl, ServiceInsight, ServicePulse and the bus stops
NServiceBus requires a license which must be updated yearly to remove warnings on expired licenses in the Particular applications and event logs.
Licenses can be requested from the ADOS Support team here.
The license should be updated in:
• ServiceControl Management.
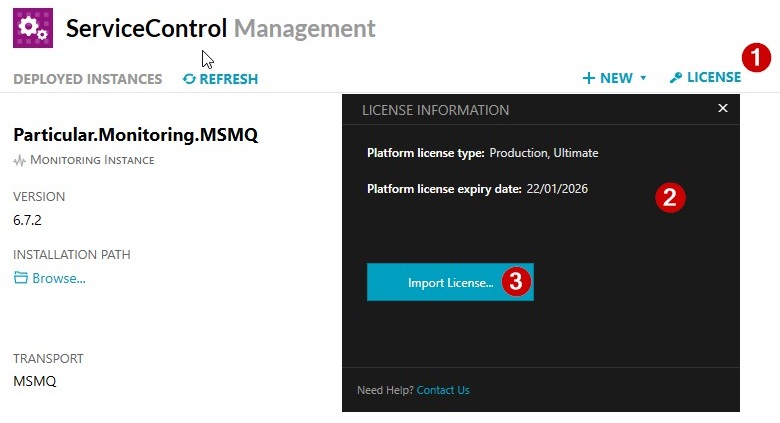
Open Service Control Management (Particular.ServiceControl-x.x.x.exe) and click the License button (1).
A License Information dialog (2) will open.
Press the Import License… button (3).
Browse to the license XML file and press Open. The license expiry date will change and the License Information dialog can be closed using the ‘X’ in the upper right corner.
The ATS Bus bus stop installation directory (e.g. C:\Program Files\ATS Global\ATS Bus\Bus Stops.3.4.25297.2\AdosBusStop) for every bus stop contains a subdirectory named License that contains the NServiceBus license file. The new license should overwrite the old one. The bus stops do not have to be restarted immediately, but the bus stop will show license expiry messages in the log files until then if the particular license is already expired.
For further information on license behaviour, please click here.
Setup a Monitoring Instance
Perform the following steps to setup a ServiceControl Monitoring instance:
Open the ServiceControl management application.
The following window opens.
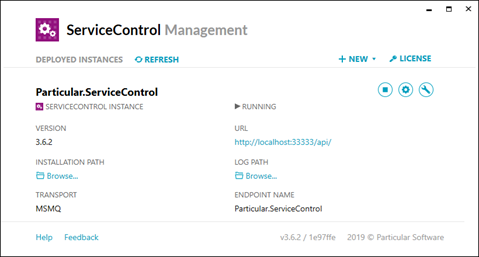
It may or may not show already configured ServiceControl or monitoring instances.
Click +NEW and select Add monitoring instance.
In the new window enter the required information. The transport selected should be the same as the transport used by the bus stops and the ServiceControl instance.
Click Add once all configuration items are provided.
Setup an error and audit instance
Run Service Control Management.
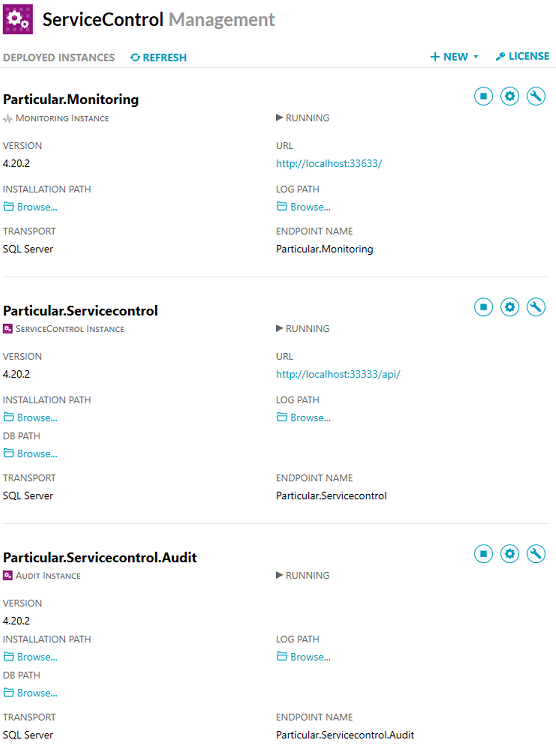
Older versions of ServiceControl managed audit, error and control messages. ServiceControl version 4.20.2 separates the audit message handling from the error and control message handling and requires the user to configure 2 separate instances. The instances should use the following preferred configuration values:
Transport: RabbitMQ, Azure Service Bus, Azure Storage Queues or SQL Server Transport. This depends on the transport used by ATS Bus.
Audit retention: 2 days. The value could be set to a higher value but that requires more disk space to be used by the embedded ServiceControl database. The approximate storage capacity required depends on the amount of messages being audited * their message size * the retention time.
Error retention: 5 days. This gives the user 5 days to detect errors and retry the messages using ServicePulse or ServiceInsight. The value could be set to a higher value but that requires more disk space to be used by the embedded ServiceControl database. The approximate storage capacity required depends on the amount of messages being audited * their message size * the retention time.
Instance name: The name of the ServiceControl instance. It allows the user to configure a meaningful name for the instance that is shown in the Windows Services application.
The name of the ServiceControl instance is used as the ServiceControl queue name. The name for the ServiceControl instance must match the ‘ServiceControl queue’ in the general NServiceBus configuration in ATS Bus Cockpit.
Audit Queue name: The name of the audit queue. It must match the ‘Audit queue’ in the general NServiceBus configuration in ATS Bus Cockpit.
Error Queue name: The name of the error queue. It must match the ‘Error queue’ in the general NServiceBus configuration in ATS Bus Cockpit.
ServicePort: The default value of the ServiceControl instance is 33333, the Audit instance uses 44444.
Database maintenance port: The default value of the ServiceControl instance is 33334, the Audit instance uses 44445.
Ensure that the drive/directory where the ServiceControl database and logfiles are store has enough storage capacity. The size of the database may exceed 100GB depending on the amount of messages being audited.
After configuration, the ServiceControl Management application may show the following instances:
Register ATS Bus application in ATS Security
Before starting the installation, the ATS Bus application needs to be registered in ATS Security.
Browse to the ATS Security URL and login with a user that has rights to edit applications.
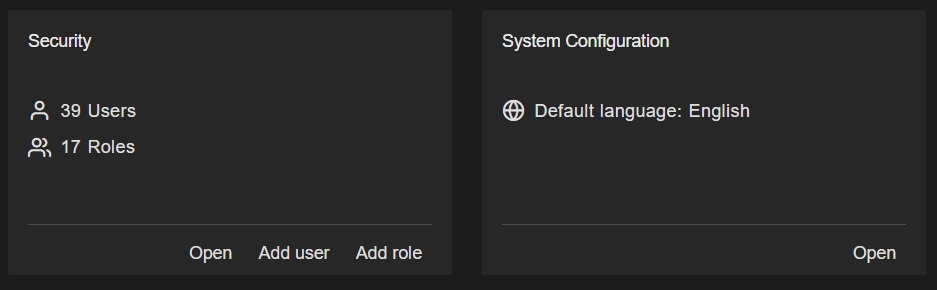
Click the Security card and press Open.
Click the Applications card and press Add Application.
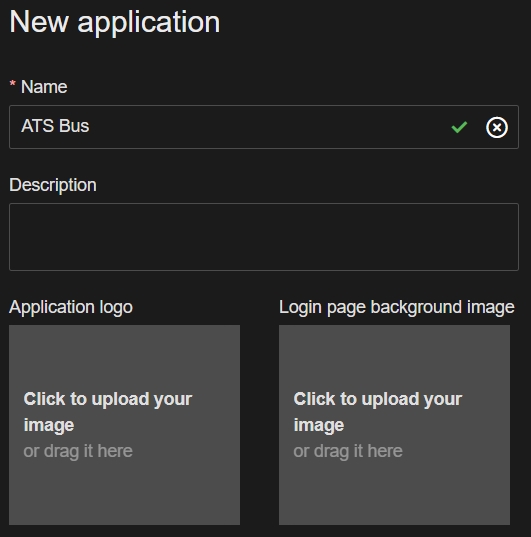
Enter the following information about the new application:
Name: Enter a name for the application, for example ATS Bus.
The name assigned to the application must be unique within ATS Security.
Description (optional): Enter a description for the application that can be seen in the applications grid card.
Application logo and/or background image (optional): Upload a logo image and/or background image for the application.
Press Add and edit.
If the application was added successfully, the pane will refresh and feature a new Application Id field and the Application status field will display Created.
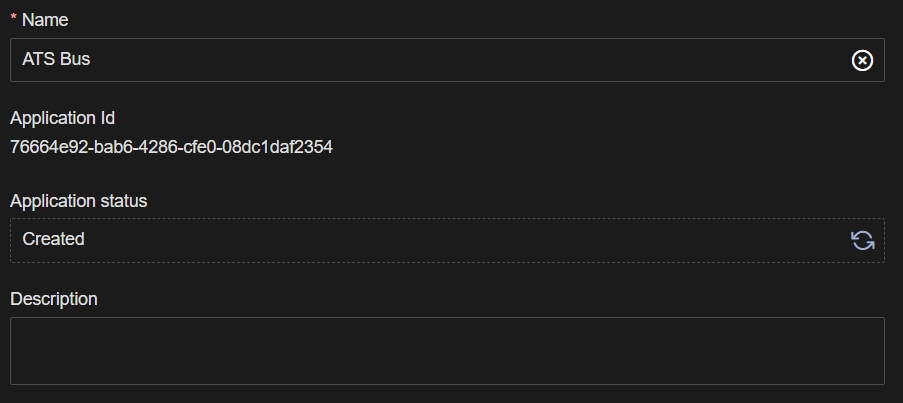
Acquire Application ID for ATS Bus application
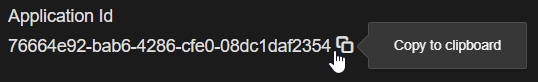
During the installation of the ATS Licensing Server services, an Application ID is required. To obtain the Application ID, hover over the Application Id field and copy the string by pressing the the copy  icon.
icon.
Install ATS Bus Data Service
This section describes the ATS Bus installation process.
Close any application that controls Windows services like services.msc, computer management and the task manager before installing ATS Bus. They may interfere with the installation procedure.
Run the installer. The following screen will be displayed:
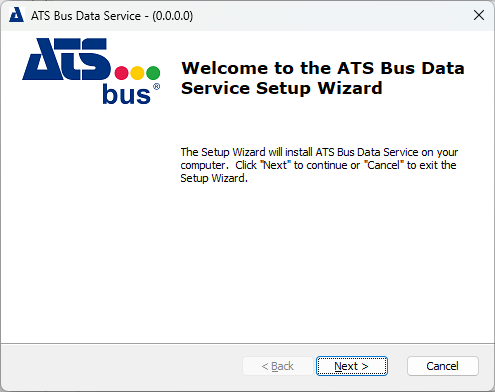
Click Next.
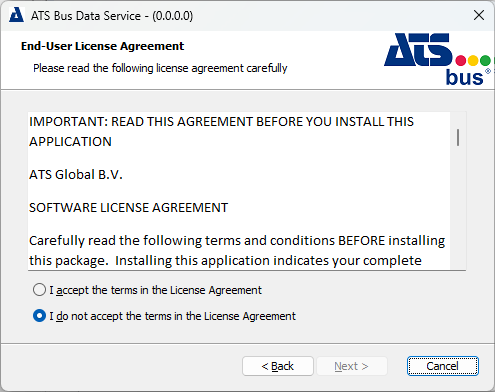
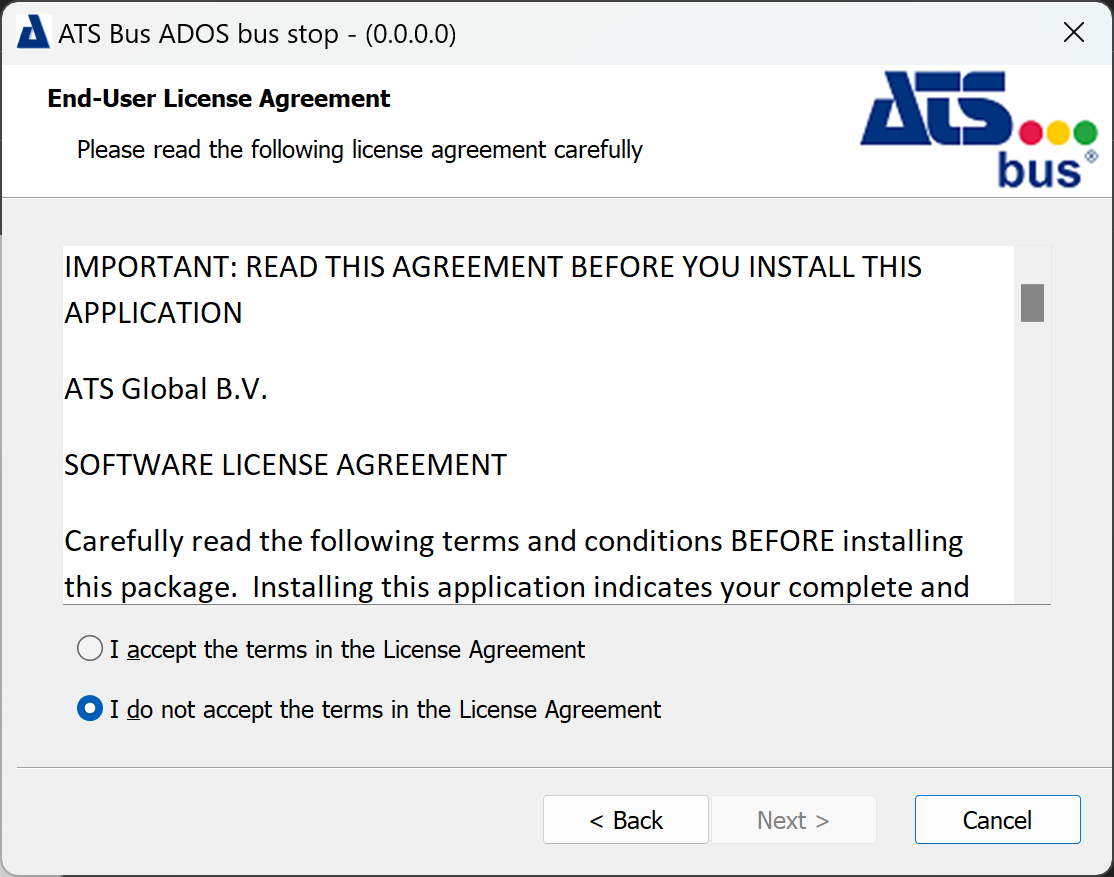
Select I accept the terms in the license agreement. Click Next.
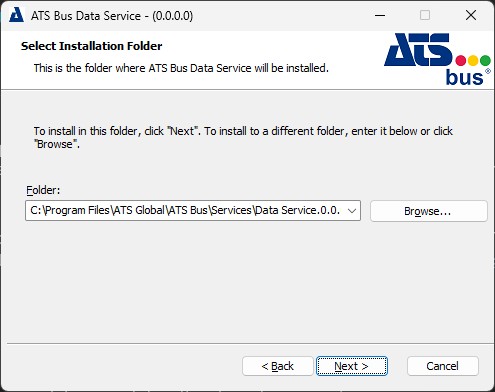
Provide the installation directory and click next.
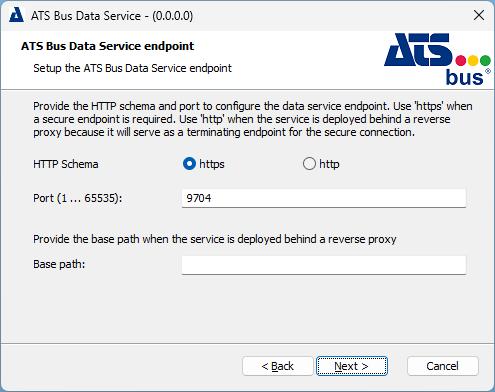
Provide the HTTP schema and port to configure the data service endpoint. Use 'https' when a secure endpoint is required.
Use 'http' when the service is deployed behind a reverse proxy because the reverse proxy will serve as a terminating endpoint for the secure connection, therefore https is not required.
The Base path is only required when the service runs behind a proxy server. The base path starts with a forward slash. E.g. /busservices/dataservice. This will yield the following endpoint: http://fqdn/busservices/dataservice.
Click Next.
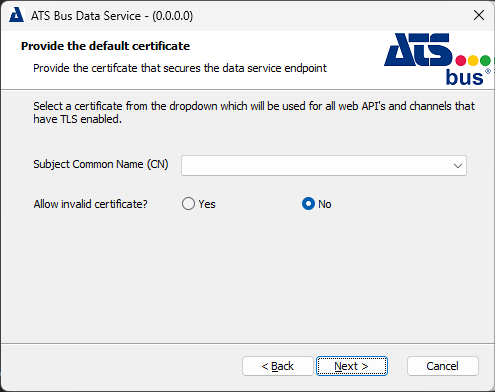
Select a certificate from the dropdown, which will be used for all web API's and channels that have TLS enabled. The dropdown shows certificates in the Personal folder that have their intended use set to Server Authentication.
Click Next.
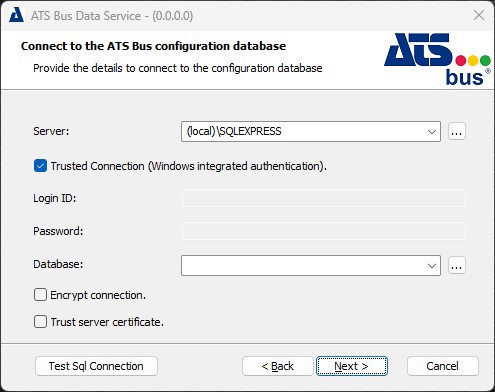
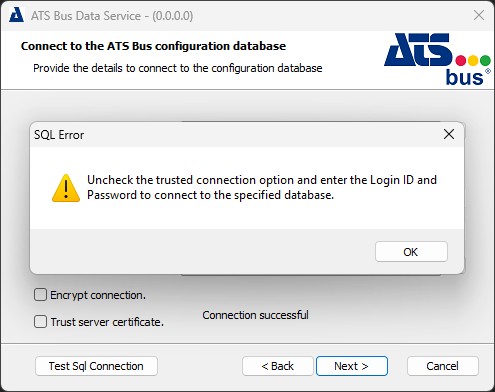
Fill in the required information to connect to the SQL Server to create a new or select an existing ATS Bus configuration database. Click on ![]() next to the Database dropdown to refresh the list of existing databases on the selected Server. The Trusted Connection checkbox should be unticked when an existing database is selected because ATS Bus requires the user to log on using SQL authentication. Pressing Next without unticking the checkbox will show the following message:
next to the Database dropdown to refresh the list of existing databases on the selected Server. The Trusted Connection checkbox should be unticked when an existing database is selected because ATS Bus requires the user to log on using SQL authentication. Pressing Next without unticking the checkbox will show the following message:
 7
7
Unchecking the checkbox will allow to provide a login and password:
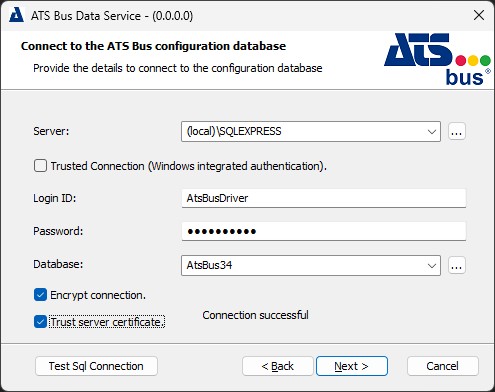
If the database name provided doesn't exist in the Database dropdown a new database will be created. Creating a new database can be done using Windows authentication and therefore the Trusted Connection checkbox can be checked. This will use the current Windows account that runs the installer to create the database.
The Encrypt connection checkbox initiates an encrypted connection with the database. This requires a valid certificate because the default self-signed certificate may raise certificate validation errors when the hostname does not match the DNS names in the certificate. To accept the SQL Server certificate, the Trust server certificate checkbox can be ticked.
Click Next.
If a new database is selected, the following dialog appears asking for the Login and password that the ATS Bus data service will use to connect to the database.
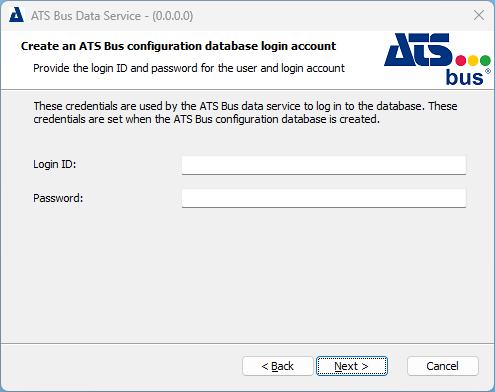
Provide a Login ID and Password.
The Login ID and Password are different from the one used to logon to ATS Bus Cockpit.
Click Next.
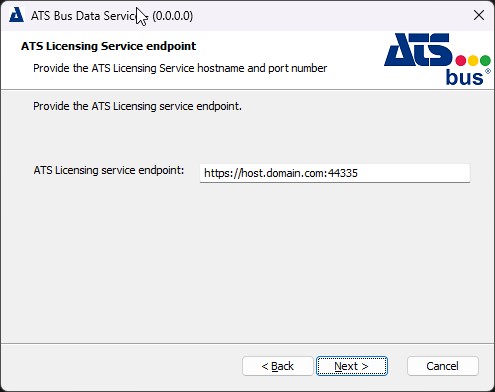
Provide the Licensing manager endpoint. Ensure to use the same hostname as configured in the SAN extension of the certificate when using HTTPS otherwise the certificate validation will fail for the hostname.
14. Click Next.
If the Database feature is not selected, the endpoint is prefilled using information from the current database.
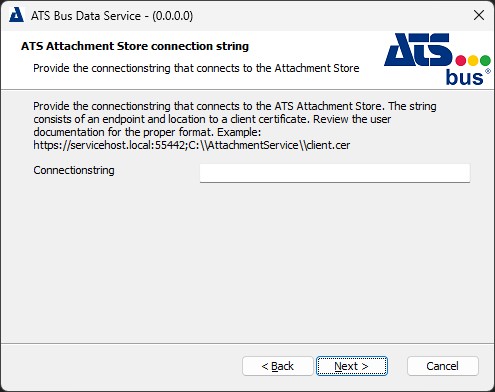
Provide a connection string as indicated in the description or leave it empty when ATS Bus will not use the FileTransfer channels. Ensure that the hostname portion of the connection string uses the same hostname as configured in the SAN extension of the certificate when using HTTPS otherwise the certificate validation will fail for the hostname.
Click Next.
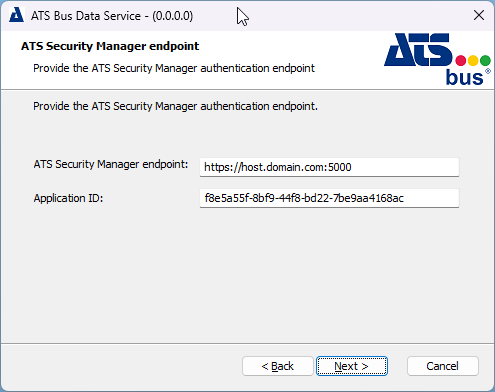
ATS Bus uses ATS Security to authenticate users. Authentication happens through an authentication endpoint and this dialog is used to provide that endpoint to the ATS Bus Data Service.
ATS Security Manager endpoint: Provide the security manager endpoint and ensure to use the same hostname as is configured in the SAN extension of the certificate when using HTTPS otherwise the certificate validation will fail for the hostname. The endpoint is formatted as https://hostname.domain:5000
If the Database feature is not selected, the endpoint is prefilled using information from the current database.
The endpoint should include the FQDN and be in the following format: https://hostname.domain:5000
Select a certificate from the dropdown, which will be used for all web API's and channels that have TLS enabled. The dropdown shows certificates in the Personal folder that have their intended use set to Server Authentication.
Application ID: Paste the application ID obtained in section Acquire Application ID for ATS Bus application.
Click Next.
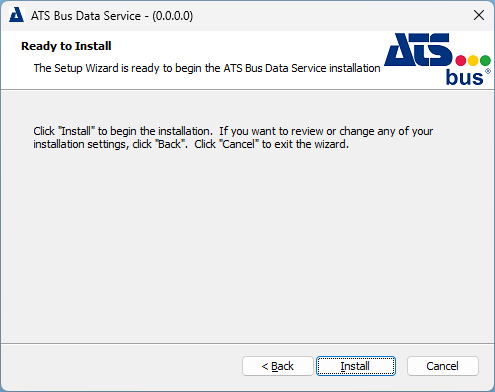
Click Install to install the ATS Bus data service.
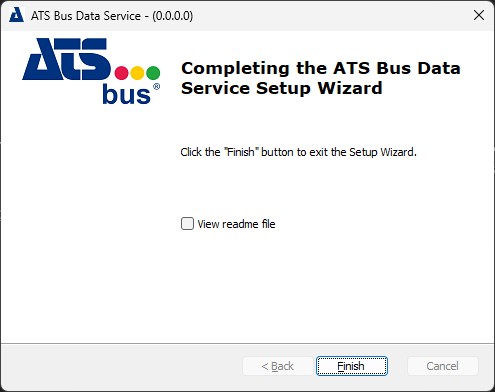
Click Finish to close the installer.
Install ATS Bus Cockpit
This section describes the ATS Bus Cockpit installation process.
Run the installer. The following screen will be displayed:
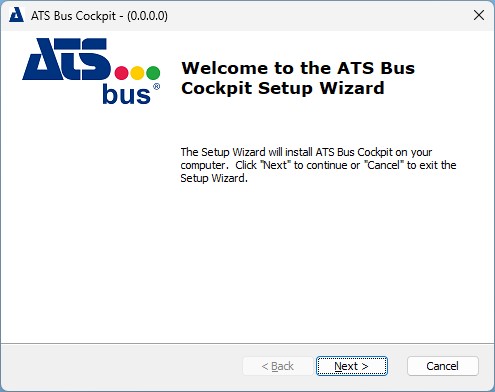
Click Next.
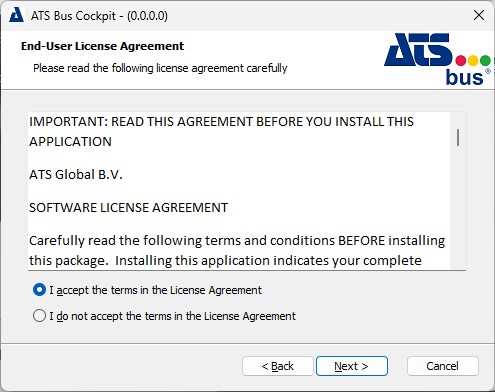
Select I accept the terms in the license agreement. Click Next.
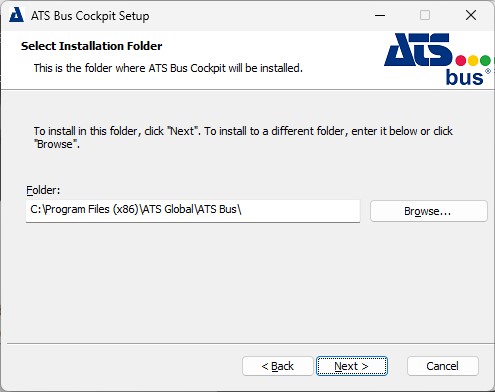
Select the installation folder for Cockpit. Click Next.
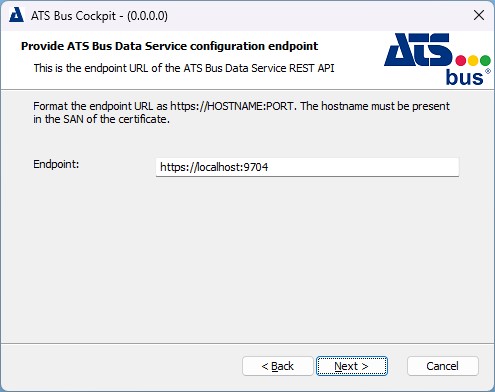
Provide the ATS Bus Data Service configuration endpoint. Click Next.
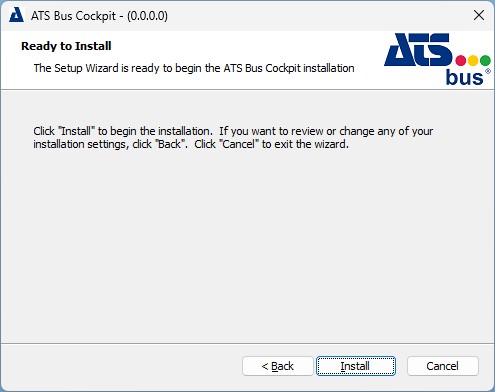
Click Install to install the application.
Click Finish to close the installer.
Configuration of roles for ATS Bus Configuration
After the successful installation of ATS Bus the status of the registered ATS Bus application in ATS Security should be set to Configuration Uploaded. This indicates that the ATS Bus application rights have been uploaded to ATS Security and can be assigned to ATS Security roles, which in turn can be assigned to users.
ATS Bus includes the following application permissions:
AtsBusConfigurationRead
AtsBusConfigurationWrite
AtsBusWorkOrderHandlingRead
AtsBusWorkOrderHandlingWrite
AtsBusMonitoringRead
AtsBusBusStopRestart
For more information on creating and managing user accounts, please visit the ATS Security online help here.
ATS Bus must be installed before ATS Security is configured.
Create an ATS Bus role
Create a new role in ATS Security i.e. ATSBusAdmin. For further information on creating user roles, click here.
Select the Rights tab and expand the ATSBus list.
Assign all permissions to the new role. For further information on editing roles, click here.
Assign the new role to a user that can authenticate through ATS Security such as an admin user. For further information on editing users, click here.
Alternatively, assign all permissions to an existing admin role.
Users assigned with the new permissions are required to log out and sign in again for the changes to take effect.
The user and role configurations are completed. The user can log into ATS Bus Cockpit using the Admin account.
Additional identity providers such as active directory can be configured to provide access e.g. via the current windows login.
Install a Bus Stop
This section describes the installation process for every Bus Stop type.
If an earlier version is present it must be uninstalled before proceeding.
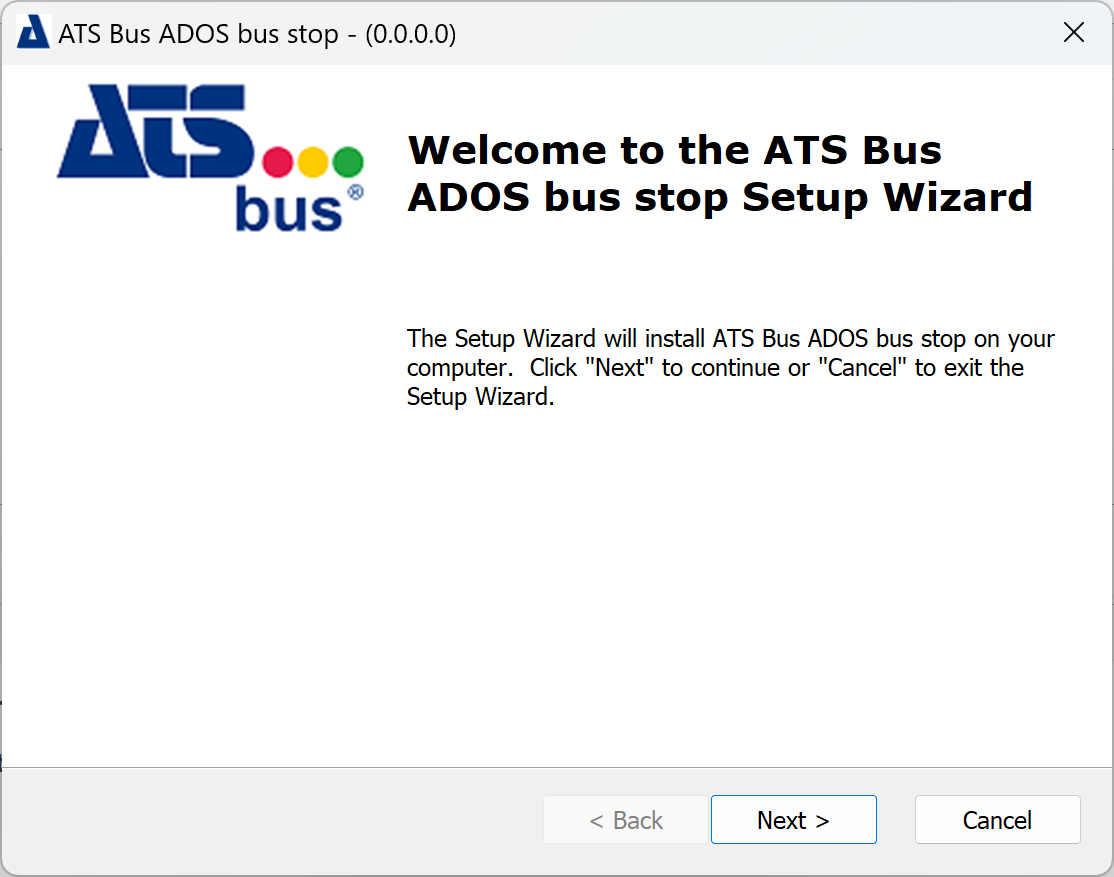
Run the installation executable and click Next.
Select I accept the terms in the License Agreement and click Next.
Select an installation folder.
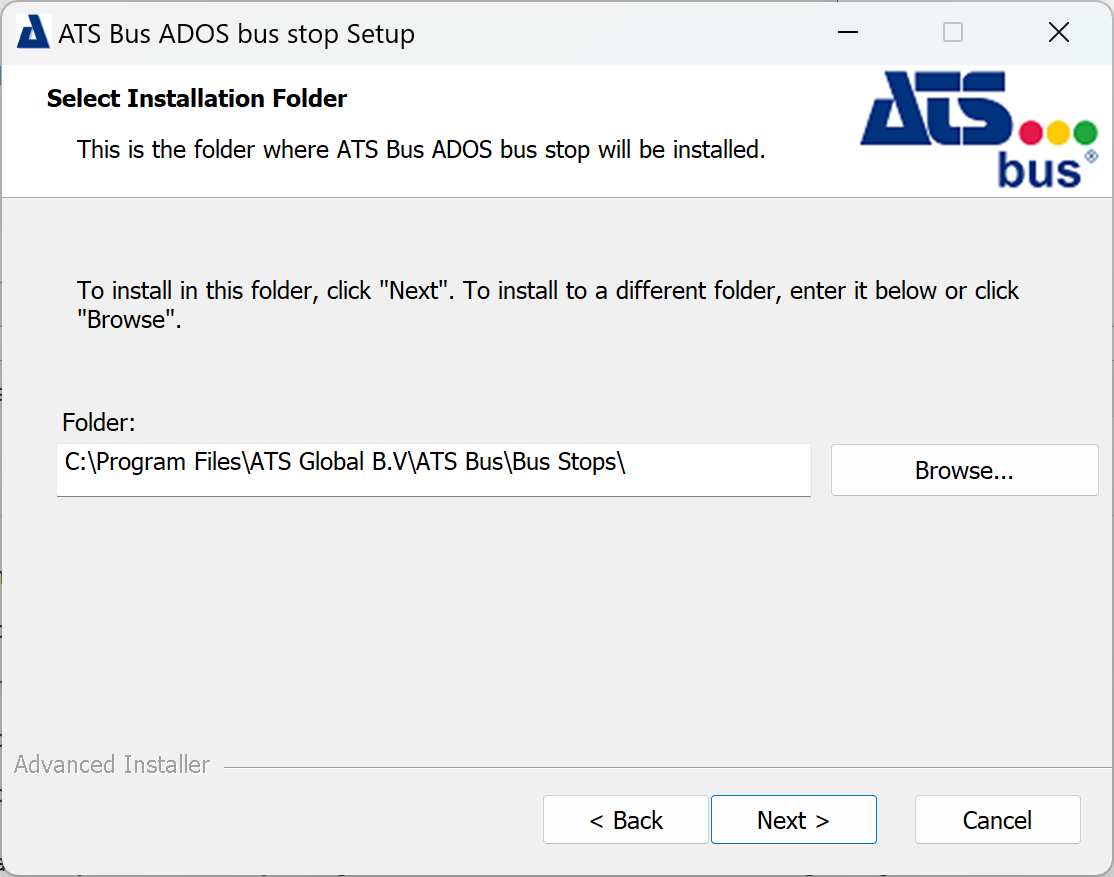
The OT, IT and ADOS bus stop install to C:\Program Files\.
The OT bus stop installer will also display a tab with a list of features under a Features tab. The installation directory can be configured in the Installation folder tab.
Click Next.
Enter the name of the bus stop. This is the name it will use during configuration.
Select Use TLS to specify that all endpoints will use TLS. This setting is configures the default certificate in the appsettings.json file.
Provide a base path if the bus stop is deployed behind a reverse proxy.
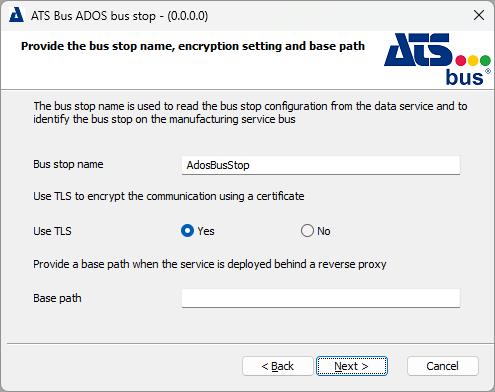
The bus stop may only contain the following characters: 'a'-'z', 'A'-'Z', '0'-'9' and '_'
This bus stop name will also be used as folder name in which the installer will copy the assemblies and configuration files of that bus stop.
Step 9 will be skipped if Use TLS is set to No.
Click Next.
This dialog allows users configure a default certificate that is used for all web API’s, which are hosted by the bus stop and have Use TLS set to Yes.
Set Allow invalid certificates to Yes if self-signed certificates are used. Also make sure to add a copy of the self-signed certificate to the Trusted Root Certification Authorities store.
Click Next.
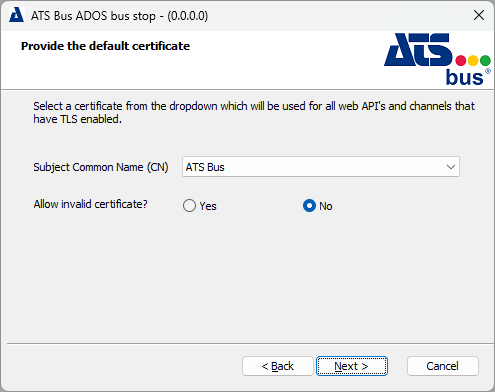
For further information on configuring certificates, please click here.
Provide the ATS Bus Data Service configuration endpoint.
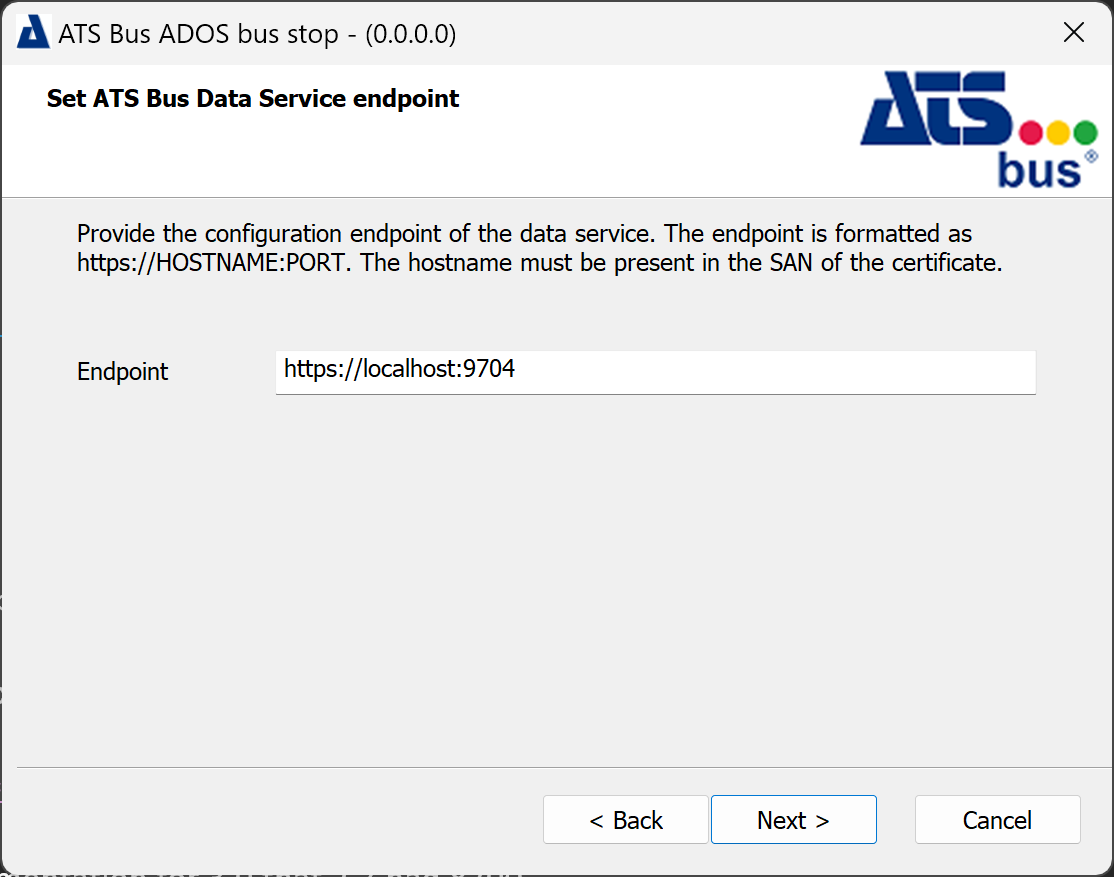
The default port of the ATS Bus 3.0 data service configuration endpoint is 9704. The hostname of the endpoint should match one of the hostnames provided in the Subject Alternative Name section of the certificate that secures the configuration endpoint.
Click Next.
Click Install.
When the application has successfully installed the following screen will be shown. Click Finish to close the installer.
The bus stop may fail to start after the installation. Please visit the troubleshooting section to resolve the issue here.
Update ATS Bus
The latest ATS Bus installers have been updated to allow multiple versions to be installed side by side. The installers will also uninstall older versions prior to installing the newer version. In additionm, ATS Bus 3.4 and 3.2 can be hosted on the same server, each with their own dedicated transport.
There are multiple upgrade scenarios:
Upgrading the same major-minor version.
Replace an older major or minor version with the new version.
Upgrade the same major-minor version
When upgrading the same major-minor version, for example 3.4.0.1 to 3.4.0.2, the new ATS Bus installers will delete the old installation automatically and overwrite it with a newer version when asked. The new installers also offer the option to keep the old installation and install the new version in parallel. The new installers still require the configuration properties to be entered because these are not read from the previous configuration. The new installer includes the version number in the name of the installation directory to differentiate between various versions being installed.
Ensure that the old services are stopped and disabled as they may interfere with the new installation. The services can be disabled or reconfigure to use different NServiceBus transports and persisters.
An SQL backup is still recommended when upgrading ATS Bus applications and services. This allows the user to roll-back when required.
Replace existing version if it is an older major/minor release
This paragraph describes how to replace and older major or minor version with this release (for example from 3.4.0.1 to 3.5.0.1 or 4.0.0.1 for example).
First, all ATS Bus services and ServiceControl instances must be stopped after all messages have been handled/processed. This can be achieved by first stopping the ‘emitting’ bus stop and then the ‘receiving’ bus stop, next the service control instances can be stopped. Please be advised that messages destined to ATS Bus are not processed and they must be resent by the peer. Upgrading ATS Bus includes upgrading the transport and therefore the transport should not have any messages queued to prevent message loss. Execute the following steps once all ATS Bus and the other services are stopped:
Stop all ATS Bus services (data service and bus stops). Stop emitting bus stops first, next stop the receiving bus stop and then stop the service control instances.
Stop all Particular services.
Backup the ATS Bus configuration database.
Upgrade ServiceControl, ServiceInsight and ServicePulse to the versions mentioned in this installation note. Please follow the upgrade guide provided at https://docs.particular.net/servicecontrol/upgrades/ when upgrading ServiceControl, ServiceInsight and ServicePulse.
When using RabbitMQ, upgrade RabbitMQ to version 4.1.4 or higher and Erlang to the version specified by https://www.rabbitmq.com/docs/which-erlang. When possible, reconfigure ATS Bus and NServiceBus to use a dedicated virtual host instead of the default one (‘/’) . This will make future upgrades easier, and it allows other configurations of services to use the same RabbitMQ instance. Virtual hosts are a logical group of connections, queues, exchanges, bindings, and permissions. It would allow to easily separate between production and test environments using the same broker. Read the blogpost https://www.cloudamqp.com/blog/what-is-a-rabbitmq-vhost.html for a detailed explanation.
Uninstall the bus stops.
Uninstall ATS Bus Cockpit and the data service.
Follow the steps provided in the ATS Bus data service, ATS Bus Cockpit and bus stop installation instructions provided earlier on in this documentation.
The ATS Bus data service installer will run a database migrator to update the ATS Bus configuration database to the latest version.
Install ATS Bus side by side with an existing ATS Bus installation
This version of ATS Bus can be installed alongside existing ATS Bus 2.8 or 3.2 installations if transport and persistence for both installations are separated. Separating transport is done:
Using separate databases for SQL transport: Isolates message queues at the database level for independent processing.
Using virtual hosts on RabbitMQ: Each virtual host provides a separate namespace, isolating exchanges, queues, and bindings to segregate different installations or environments. Read https://www.cloudamqp.com/blog/what-is-a-rabbitmq-vhost.html for more information.
Using storage accounts with Azure Storage Queues: Different storage accounts act as isolated containers for queues, ensuring that messages and processing remain separate across installations.
Using namespaces with Azure Service Bus: Each namespace represents an isolated messaging environment with its own queues, topics, and subscriptions, perfect for separating distinct deployments.
For further details see:
Azure Service Bus Configuration
Service Bus Messages
Separating persistences is done by configuring separate persisters. ATS Bus currently supports SQL and Oracle persistences meaning that each installation requires its own database to persist runtime information.
Each ATS Bus installation requires a monitoring, error, and audit instance, which obtain their information from the configured transport. These instances push their readings to a ServiceControl instance. Each ServiceControl instance provides an HTTP interface for ServicePulse and ServiceControl to visualize the captured data. ServiceControl and ServiceInsight are unable to connect to multiple ServiceControl instances so observing each installation is done by changing the endpoint configurations in ServiceControl and ServiceInsight or install a separate ServicePulse instance, so it is able to provide a second web interface to monitor each installation.
Installing ATS Bus side by side works like a standard installation, please visit the installation instructions of the ATS Bus data service, ATS Bus Cockpit and the bus stops.
Configure to Run as Local or Domain User
By default, ATS Bus services (data service, browsing service or bus stop) run under the ‘Local System’ account but IT departments may need to run the services under a dedicated user account. This document provides information on how to achieve this. The following topics will be addressed:
Running the ATS Bus services as a dedicated local or domain user.
Setting up OPC DA (Workcenter bus stop OPC DA channel).
Build-in Accounts, Users, Groups and Permissions
Applications and services require a user or build-in account to execute and access resources (objects). The following build-in accounts are often used to run services:
Local System (NT AUTHORITY\System)
Has unrestricted access to all local resources.
More powerful that Administrator account.
The Local System account uses the PC account (hostname$) to login on the remote computer if both systems are in the same domain.
The Local System account uses the ANONYMOUS LOGON account to login on the remote computer if both systems are not in the same domain.
Network Service (NT AUTHORITY\Network Service)
Has restricted access to local resources.
The Network Service account uses the PC account (hostname$) to login on the remote computer if both systems are in the same domain.
The Network Service account uses the ANONYMOUS LOGON account to login on the remote computer if both systems are not in the same domain.
Local Service (NT AUTHORITY\Local Service)
Has restricted access to local resources.
The Local Service account always uses the ANONYMOUS LOGON account to login on the remote computer.
There are 2 types of user account, a local account and a domain account. A local account only has access to local computer resources and a domain account can be used to authenticate a domain user on multiple systems within a domain. In a workgroup configuration, machines cannot resolve each other’s local accounts because they do not share the same security database. Therefore, remote users are authenticated using the ANONYMOUS LOGON account.
A group is a collection of users and it simplifies the administration of user rights. Users inherit their rights from a group if they are a member of that group. The build-in group ‘Everyone’ represents local and domain accounts that the local computer knows.
Permissions apply to objects like files, services and so on and can be granted to domain (and trusted domain) users, groups and local users and groups (of the computer where the object is located). Permissions will indicate if a user or group can perform a specific operation on that object e.g. Execute permission can be assigned to a specific group, then only members of that group can execute that service. Other users that are not members of that specific group are denied the ability to execute the service. A user of that group can be denied permission by explicitly denying the permission for that user.
Follow the guidelines below when updating permissions:
Permissions on local objects (files, directories and queues) do not have to change when all ATS Bus services run as LOCAL SYSTEM on one single computer, this account has enough privileges to access all objects on the local computer.
Permissions for local objects should change when ATS Bus services run under a local or domain user account. Object permission must include this user account.
Remote object permissions (shares, queues, etc…) must include the:
computer account (hostname$) of the system that runs the ATS Bus services as LOCAL SYSTEM when working from within a domain.
the domain user account of the user that runs the ATS Bus services in a domain.
the ANONYMOUS LOGON account when the ATS Bus services use local computer accounts. Remote nodes cannot authenticate local users since they reside in other security databases.
How to Change File and Directory Permissions
Changing file and directory permissions are handled by the security tab in the file or directory property dialog.
Use the windows file explorer to navigate to the file or directory and use the context menu to bring up its properties.
Select the Security tab.
Click Edit to add/remove users or groups from the object permissions.
Click Add to add a computer, local, domain or ANONYMOUS LOGON account.
Make sure Computers is in the list of object types. If it isn't click Object Types to add it.
Click Locations… to select the location where the account may reside.
Click Check Names… to verify if the entered account exists.
Click OK to return to the previous dialog.
Set the permissions for the account that has been added.
Make sure that all groups and users listed in this dialog should be there and click OK to return to the properties dialog.
Click OK to confirm the changes and close the properties dialog.
Sub directories inherit permissions from parent directories. Files inherit permissions from the parent directories.
How to Change File Sharing Permissions
Directory sharing permissions are handled in the sharing tab in the directory property dialog.
Use Windows file explorer to navigate to the directory you want to share and use the context menu to bring up its properties.
Click Share in the Sharing tab and a dialog appears that allows accounts to be added.
Enter the following:
<AccountName>: Local or domain user account.
ANONYMOUS LOGON: The Anonymous logon account.
<COMPUTERNAME>$: Add a computer account.
Click Share. The directory sharing dialog opens.
This action modifies the share permissions and underlying file system permissions. The Advanced Sharing… button only modifies the sharing permission and not the underlying file system permissions. For more information visit the Technet website.
How to Run the ATS Bus Services Using a Dedicated Local or Domain Account
Make sure you have permissions allowing you to update service properties.
Go to the Services dialog (press WIN + R and enter services.msc)
Right click the ATS Bus service (bus stop, data service, browsing service) and select Properties from the context menu.
Select the Log On tab, select the This account radio button and click Browse to browse for the dedicated ATS Bus user account that has been created.
Enter the password for the user and click OK.
Stop the ATS Bus service. Do not restart the service because more changes are required:
File and directory permissions must be updated for the bus stops for the following files and directories:
C:\Program Files (x86)\Applied Tech Systems\ATS Bus Bus Stop\<XXX>\instance-mapping.xml’ where <xxx> resembles the bus stop name. This file may be moved to another location in the future.
All files and folders under C:\ProgramData\Applied Tech Systems\ATS Bus\<XXX>. <XXX> resembles the bus stop name.
Network sharing permission must be changed for:
The attachments directory which is located at: C:\ProgramData\Applied Tech Systems\ATS Bus\<XXX>\Attachments. The directory should be shared and access must be allowed to the ANONYMOUS LOGON account.
The Permissions of the NServiceBus DataBus file share must contain the proper permissions. The share name is configured in the ATS Bus configuration database.
The ATS Bus service can be started after the previous items have been addressed.
